INTERPOL has taken down more than 45,000 malicious IP addresses and servers used to run phishing scams, spread malware, and launch ransomware attacks, in a coordinated six-month operation that included Nigeria among 72 participating countries and territories.
The operation, codenamed Synergia III, ran from July 18, 2025 to January 31, 2026. By the time it wrapped, 94 suspects had been arrested across multiple countries, with another 110 still under active investigation. Investigators also seized 212 electronic devices and servers during raids.
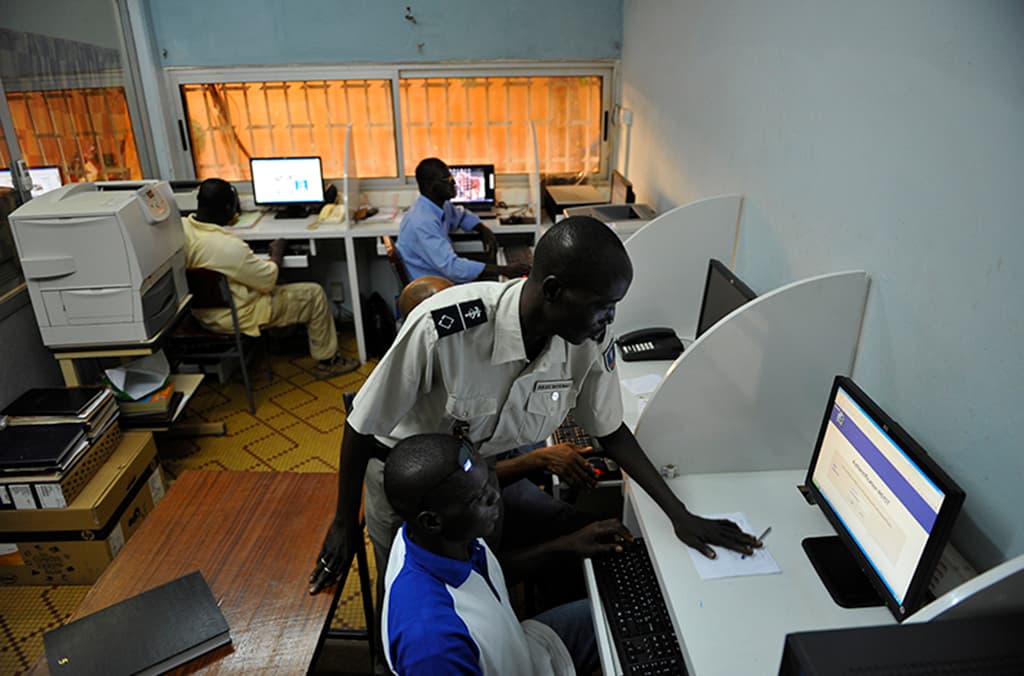
Nigeria Is Both Target and Participant
Nigeria’s position in this operation is worth sitting with for a moment. The country was not just a cooperating law enforcement partner. It is also one of Africa’s most attacked nations when it comes to ransomware.
According to INTERPOL’s Africa Cyberthreat Assessment, Nigeria recorded about 3,459 ransomware detections in 2024, placing it third on the continent for ransomware exposure. That is not a small number. For context, that is detections in a single year, across a digital economy that is still maturing and, in many places, still underprotected.
At the same time, Nigerian authorities have been contributing to enforcement actions. In a separate but related regional operation, 130 suspects linked to cyber-enabled fraud, including fake online casino schemes and investment scams targeting victims in other countries, were arrested with Nigerian law enforcement’s involvement.
The dual reality is this: Nigeria is a target, and Nigeria is fighting back. Both things are true at the same time.
How the Operation Ran
Synergia III was not a blunt instrument. INTERPOL processed threat intelligence from partner organizations into specific, actionable leads, then coordinated with national agencies to act on them simultaneously across different jurisdictions. The sequencing mattered. If you tip off one country before others are ready, suspects migrate infrastructure overnight. Global coordination prevents that.
Three private cybersecurity firms, Group-IB, Trend Micro, and S2W, worked alongside INTERPOL throughout the operation to track malicious servers and map criminal infrastructure before raids happened.
The result was a series of coordinated national actions: raids on key locations, server shutdowns, device seizures, and the dismantling of networks that had, in some cases, been operating across multiple continents at once.
What Investigators Found
The findings from individual countries paint a picture of how sophisticated and diverse cybercrime operations have become.
In Macau, China, authorities uncovered more than 33,000 phishing and fraudulent websites. Many were built to impersonate legitimate platforms: banks, government portals, payment service providers. Victims were either tricked into topping up accounts on fake sites or into handing over personal and credit card information without realising the sites were not real.
In Togo, police arrested 10 suspects who had been running a fraud ring out of a residential building. The group divided up the work. Some members hacked into social media accounts. Others used those compromised accounts to run romance scams and sextortion schemes against the account owners’ contacts. It was organised, structured, and deeply human in how it exploited trust.
The Broader Pattern
Synergia III is the third phase of an ongoing INTERPOL initiative targeting cybercrime infrastructure. It builds on earlier operations in the series, as well as related crackdowns like Red Card 2.0, which focused specifically on Africa and recovered over $4.3 million linked to cybercrime activities across 16 African countries, including Nigeria and Kenya. That operation led to 651 arrests and the seizure of more than 2,341 electronic devices.
Neal Jetton, INTERPOL’s Director of the Cybercrime Directorate, put it plainly: “Cybercrime in 2026 is more sophisticated and destructive than ever before.” He added that the organisation intends to remain active in uniting law enforcement agencies and private sector partners to dismantle criminal networks and protect victims globally.
Several investigations from Synergia III are still ongoing.
What This Means for the Region
Operations like this rarely end cybercrime. The networks are decentralised by design. Shut down one cluster of servers, and operators shift to new IP ranges, new hosting environments, new proxy layers. Law enforcement knows this. The goal is not permanent elimination. It is sustained disruption, intelligence collection, and the gradual erosion of infrastructure that criminals depend on.
For Nigeria and the rest of Africa, that matters. The continent’s digital economy is growing fast, and cybercrime scales with it. Participation in operations like Synergia III is not just about optics. It is about whether African countries are building the institutional capacity to protect their citizens and cooperate on threats that do not respect borders.
At 3,459 ransomware detections in a single year, Nigeria cannot afford to be passive about the answer to that question.















 and then
and then